Cybersecurity is no longer optional; it’s a necessity for businesses, professionals, and individuals alike. As cyber threats continue to evolve, the demand for beginner-friendly cybersecurity training programs is growing rapidly, and to create such programs, it is extremely crucial to follow instructional design standards.
The Real Challenge
Subject matter experts understand cybersecurity and want to build a complete online course, but they often struggle with:
- Instructional design
- SCORM packaging
- LMS compatibility
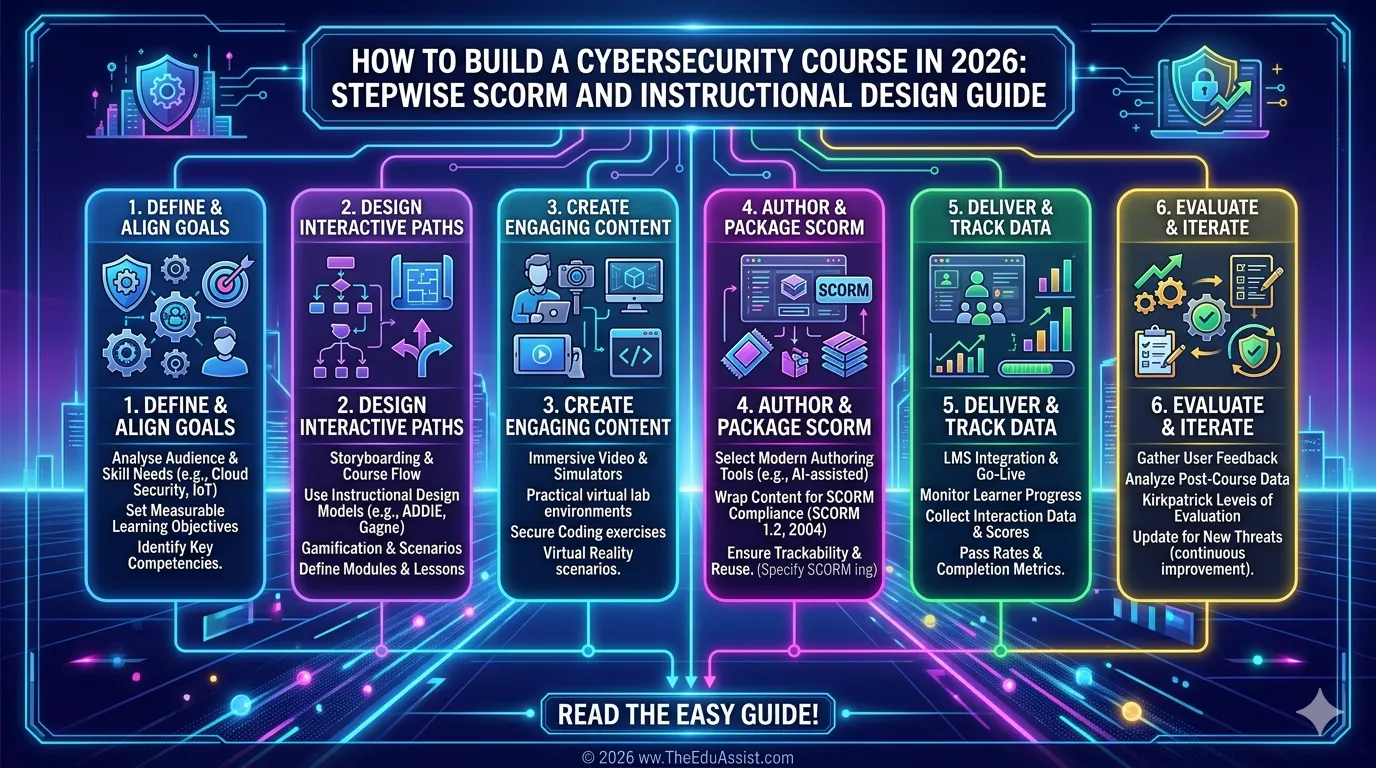
Creating a professional cybersecurity course in 2026 requires more than just content. It demands structured curriculum development, interactive learning design, and platform-ready delivery.
This guide walks you through how to build a ready-to-sell cybersecurity course using SCORM, LMS tools, and modern eLearning strategies.
Why Most Cybersecurity Courses Fail
Many cybersecurity courses fail because they are:
- Overly technical for beginners
- Lacking interactivity
- Poorly structured
- Not aligned with real-world applications
Research in cybersecurity education shows that interactive, scenario-based learning significantly improves learner engagement and skill retention.
This aligns with eLearning trends in 2026, where learners expect:
- Practical skills
- Real-world simulations
- Interactive modules
Without these elements, even high-quality content fails to deliver results.
Define the Course Outcome First (Not the Content)
Before building your course, clearly define the transformation you want to create.
Instead of: “Teach cybersecurity basics”
Define: “Enable learners to identify, prevent, and respond to common cyber threats.”
Your target audience may include:
- Beginners
- Career switchers
- Small business owners
- Non-technical professionals
Clear learning outcomes guide every decision in instructional design and content development.
Step 1: Design a Structured Curriculum (9-Module Framework)
A well-structured course ensures logical progression from awareness to mastery.
Recommended 9-Module Curriculum
| Module | Focus |
|---|---|
| 1 | Intro to Cybersecurity |
| 2 | Common Digital Threats |
| 3 | Risk Management Basics |
| 4 | Passwords & Security Layers |
| 5 | Cybersecurity Tools |
| 6 | Social Media & Mobile Security |
| 7 | Security Awareness |
| 8 | Career Paths |
| 9 | Final Simulation |
This structure moves learners from basic awareness to practical application and real-world simulation.
Step 2: Apply Instructional Design for Beginners
Cybersecurity concepts must be simplified without sacrificing accuracy.
Best Practices:
- Use simple, clear language
- Include real-life examples
- Provide visual explanations
- Follow progressive learning (simple → complex)
This approach follows modern custom eLearning principles tailored for non-technical learners.
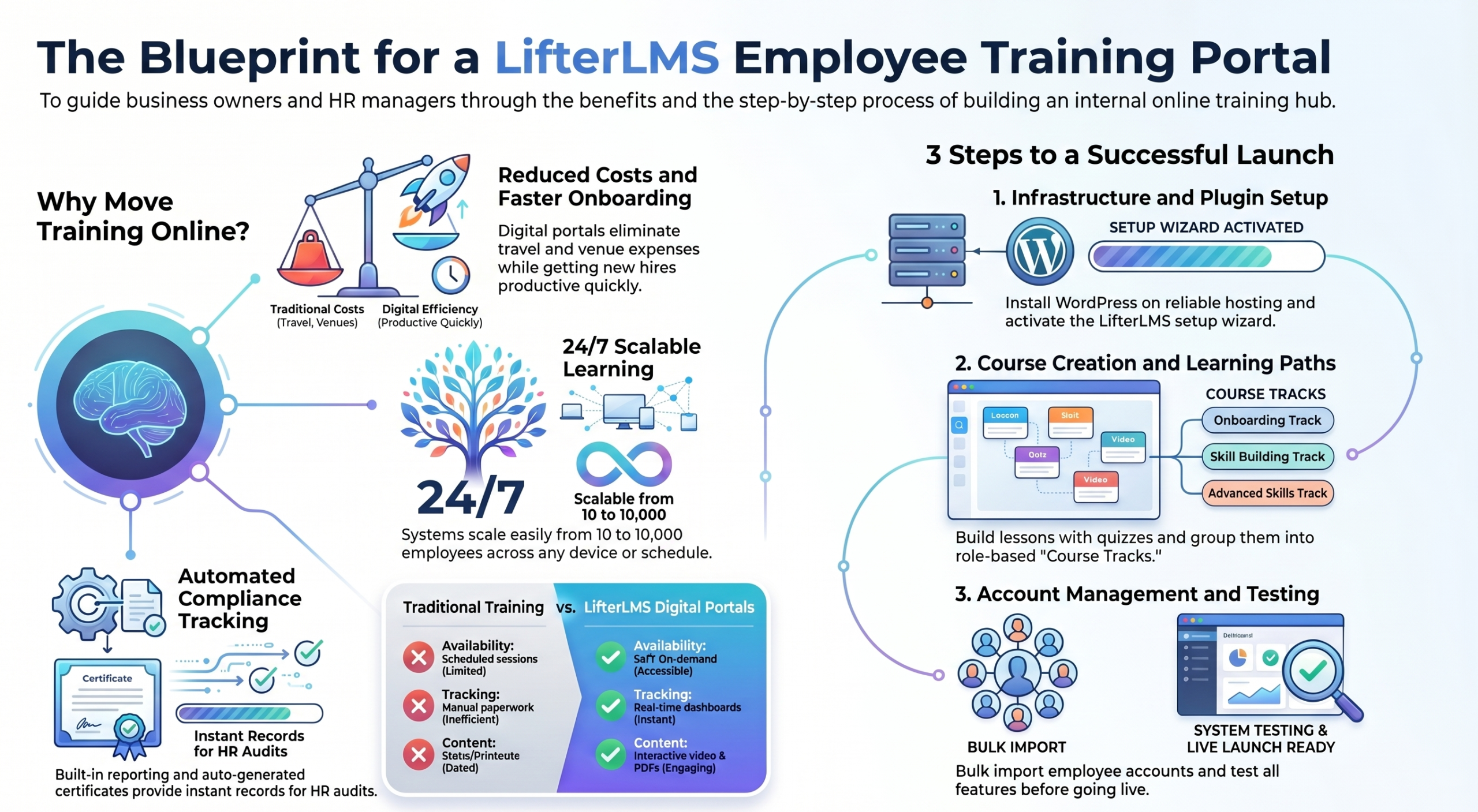
Step 3: Build Interactive SCORM/xAPI Modules
Interactivity is essential in cybersecurity training.
Recommended Authoring Tools
- Articulate Storyline
- Articulate Rise 360
Use these tools to create:
- Realistic simulations
- Decision-based scenarios
- Interactive quizzes and branching activities
Benefits of SCORM and xAPI:
- Track learner progress
- Record detailed interactions
- Seamless integration with most LMS platforms
Studies confirm that interactive cybersecurity training improves decision-making and threat recognition skills.
Step 4: Create Multi-Format Learning Content
Each module should include a mix of content types to support different learning styles:
- Explainer video
- Interactive lesson
- Quiz (3–5 questions)
- Downloadable resource (checklist, cheat sheet, or template)
This combination improves retention and encourages practical application.
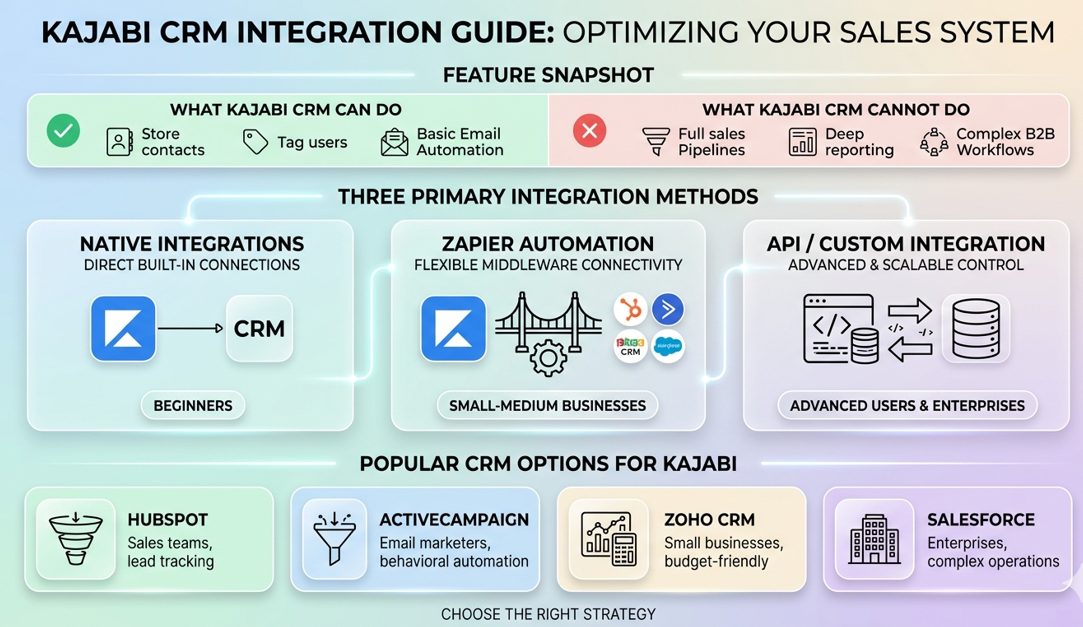
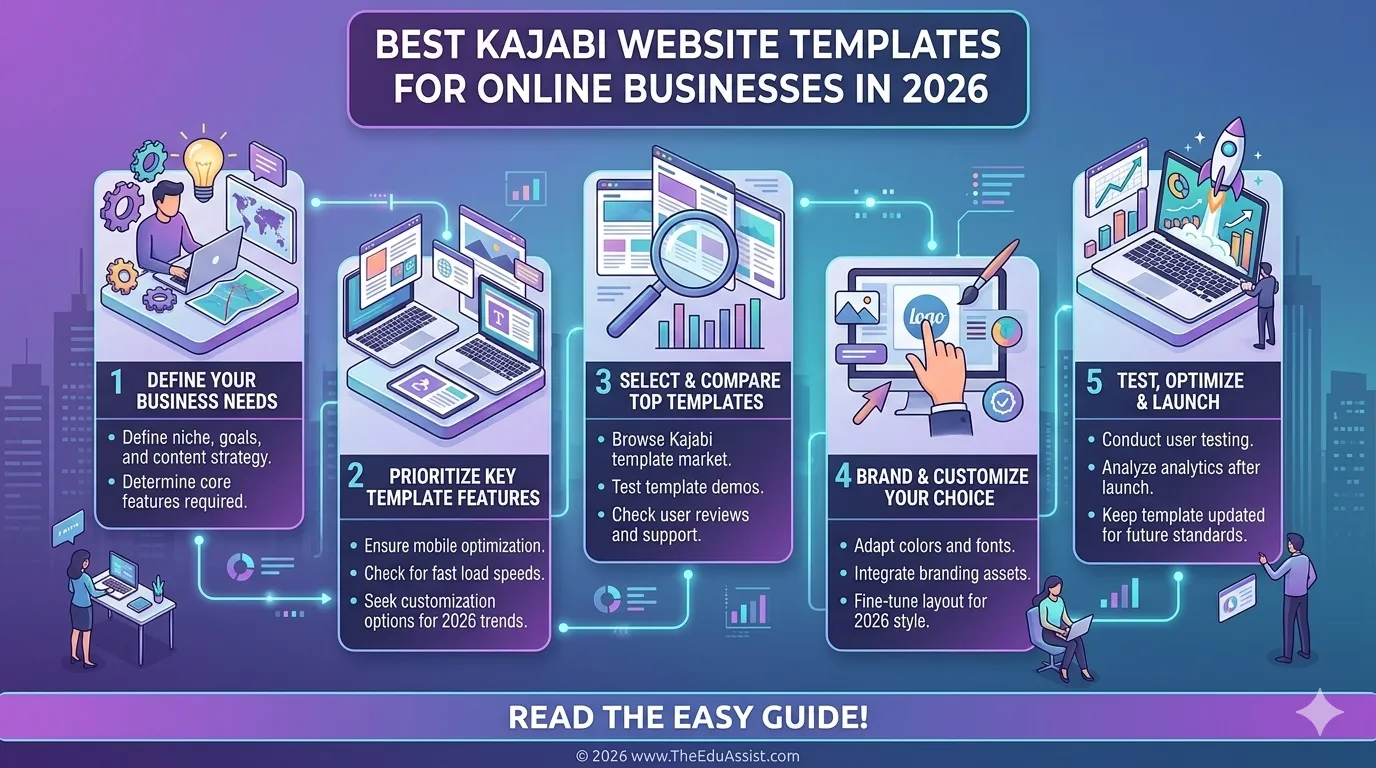
Step 5: Ensure LMS Compatibility
Your course must work smoothly across multiple platforms.
Popular LMS Platforms
| Platform | Best For | Key Advantage |
|---|---|---|
| Thinkific | Structured courses | Strong SCORM compatibility |
| Kajabi | Course businesses | Built-in marketing tools |
| Podia | Simple delivery | Easy setup |
Tips for compatibility:
- Export as SCORM packages for tracking
- Provide MP4 fallback versions
- Include LMS-native quizzes where needed
Step 6: Add Scenario-Based Cybersecurity Training
Cybersecurity is best learned through real-world scenarios.
Example Scenarios
- Phishing email simulation
- Password breach response
- Data protection case study
Benefits:
- Learners apply knowledge immediately
- They practice decision-making
- They understand the consequences of choices
Scenario-based learning is one of the most effective methods in cybersecurity education.
Step 7: Optimize for Mobile and Accessibility
Modern learners access content on multiple devices.
Must-Have Optimizations:
- Fully mobile-responsive design
- WCAG accessibility compliance
- Clear navigation and intuitive interface
These improvements lead to higher completion rates and better learner satisfaction.
Cost Reality Check: Building a Cybersecurity Course
| Category | Estimated Cost |
|---|---|
| Instructional Design | $3,000 – $8,000 |
| SCORM Development | $2,000 – $7,000 |
| Video Production | $1,500 – $5,000 |
| LMS Setup (monthly) | $39 – $199/month |
Investing in professional custom eLearning development and consulting ensures higher quality and better scalability.
Unique Perspective: Cybersecurity Training as “Behavior Change Learning”
In 2026, effective cybersecurity training goes beyond knowledge delivery; it focuses on behavior change.
Successful courses emphasize:
- Building secure habits
- Improving daily awareness
- Reinforcing smart decision-making
This approach ensures learners don’t just understand threats; they actively prevent them.
Final Thoughts
Building a cybersecurity course is not just about teaching concepts. It’s about creating practical, interactive, and scalable learning experiences.
By combining:
- Strong instructional design
- SCORM/xAPI interactivity
- Structured curriculum
- LMS compatibility
- Real-world scenarios
You can create a course that is engaging, effective, and ready for the market.
Platforms like theeduassist.com offer edu-assist consulting services to help creators build professional cybersecurity courses with expert instructional design and seamless content development.
References:
- https://www.sciencedirect.com/science/article/abs/pii/S0920548905000668
- https://www.researchgate.net/publication/320946690_Interactive_Cybersecurity_Defense_Training_Inspired_by_Web-based_Learning_Theory
- https://www.researchgate.net/publication/334066260_Supporting_cybersecurity_education_and_training_via_LMS_integration_CyLMS
FAQs
What is SCORM in eLearning?
SCORM is a technical standard that allows eLearning content to be tracked and delivered consistently across different Learning Management Systems (LMS).
Why is interactivity important in cybersecurity training?
Interactive learning significantly improves decision-making skills and threat recognition, leading to better real-world performance.
Which tools are used to create SCORM courses?
Popular tools include Articulate Storyline and Articulate Rise 360.
Which LMS platforms support cybersecurity courses?
Thinkific, Kajabi, and Podia are among the most commonly used platforms.
How can TheEduAssist help build cybersecurity courses?
Through their edu-assist consulting services, theeduassist.com helps course creators design custom eLearning cybersecurity programs with proper SCORM integration and LMS deployment.
Authored By: Sofia Arif