Cybersecurity is no longer a niche IT topic it is a core literacy for every organization and every learner. Yet most cybersecurity training is still generic, forgettable, and misaligned with real roles and risks. This disconnect creates a dangerous gap between knowing what cybersecurity means and doing the right thing in a real‑world incident.
In this article, we’ll show instructional designers how to build a Curriculum Design course that turns cybersecurity from abstract jargon into behavior‑driven, role‑specific learning experiences. By grounding your course in research from ScienceDirect, SpringerLink, and leading education‑technology journals, you empower e‑learning designers to create impactful training that improves behavior, not just test scores.
1. Why Cybersecurity Needs Specialized Curriculum Design
Cybersecurity education is not just “IT with extra steps.” Research shows that traditional, lecture‑heavy courses often fail to produce measurable improvements in real‑world security behavior, especially in non‑technical audience.
By contrast, cybersecurity curricula that are learner‑centered, outcome‑driven, and aligned with industry roles consistently yield better knowledge retention and risk‑mitigation practices.
Instructional designers need:
- A role‑based framework (e.g., “awareness user,” “security analyst,” “governance professional”).
- A curriculum design model that tightly connects learning outcomes, activities, and assessment.
- Evidence‑based pedagogical strategies drawn from educational technology and cybersecurity education research.
2. Define the Who, What, and Why of Your Course
Before you sketch a storyboard or open an LMS, clarify your course’s identity.
2.1 Target Audience
Typical learners for a Cybersecurity Curriculum Design course include:
- e‑Learning instructional designers in corporate L&D, higher education, or government training.
- Cybersecurity training specialists creating awareness programs for non‑technical staff.
- Academics or consultants designing Cybersecurity degree or certificate programs.³ ⁴
You can segment them as:
- Beginner: Strong ID skills but limited Cybersecurity background.
- Intermediate: Some exposure to security training (e.g., phishing awareness, compliance).
- Advanced: Already designing Cybersecurity modules but need stronger pedagogy and role‑specific design.³
2.2 Learning Outcomes Using Constructive Alignment
Modern Cybersecurity education research emphasizes constructive alignment: when outcomes, teaching activities, and assessment are tightly linked, learners show better performance and confidence.³
Example high‑level outcomes for your course:
- Analyze a cybersecurity role or audience profile and translate it into measurable learning objectives.
- Map Cybersecurity content (e.g., phishing, NIST CSF, Zero‑Trust) to evidence‑based instructional‑design models.
- Design formative and summative assessments that measure real‑world security practice, not just recall.³
3. Instructional Design Models for Cybersecurity Education
Use research‑backed models, then adapt them for e‑learning designers.
3.1 Core Instructional Models
- ADDIE / SAM remain widely used in Cybersecurity education and training, but studies stress that fast iteration and learner feedback are critical in a fast‑changing threat landscape.
- Constructive alignment (Biggs) is explicitly used in Cybersecurity‑related postgraduate curricula to ensure every activity supports a specific outcome.
- Backward design (Wiggins & McTighe) starts from “What should learners do in a real security incident?” and designs content backward from that.
Position your course as teaching:
- How to adapt ADDIE / SAM for Cybersecurity projects (e.g., frequent threat‑model updates, regulatory changes).
- How to apply constructive alignment to Cybersecurity outcomes (behavioral, cognitive, and cultural).
3.2 Cognitive Load and Multimedia Principles
Cybersecurity topics are dense and technical, so rely on cognitive load theory and multimedia design:
- Dual Coding and contiguity principles combine clear visuals (e.g., attack‑path diagrams, password‑hygiene flowcharts) with concise narration to reduce cognitive overload.⁵
- Universal Design for Learning (UDL) helps create accessible Cybersecurity content for mixed‑ability audiences.⁵
Show practical patterns:
- When to use simulations vs. video lectures for phishing or ransomware scenarios.
- How to chunk complex frameworks (e.g., NIST, ISO 27001) into Cybersecurity micro‑learning modules.⁴
4. Role‑Based, Market‑Aligned Cybersecurity Content
Cybersecurity curricula often lag behind job roles and threats. A strong Cybersecurity Curriculum Design course trains instructional designers to reverse‑engineer curricula from roles and risk landscapes.³ ⁴
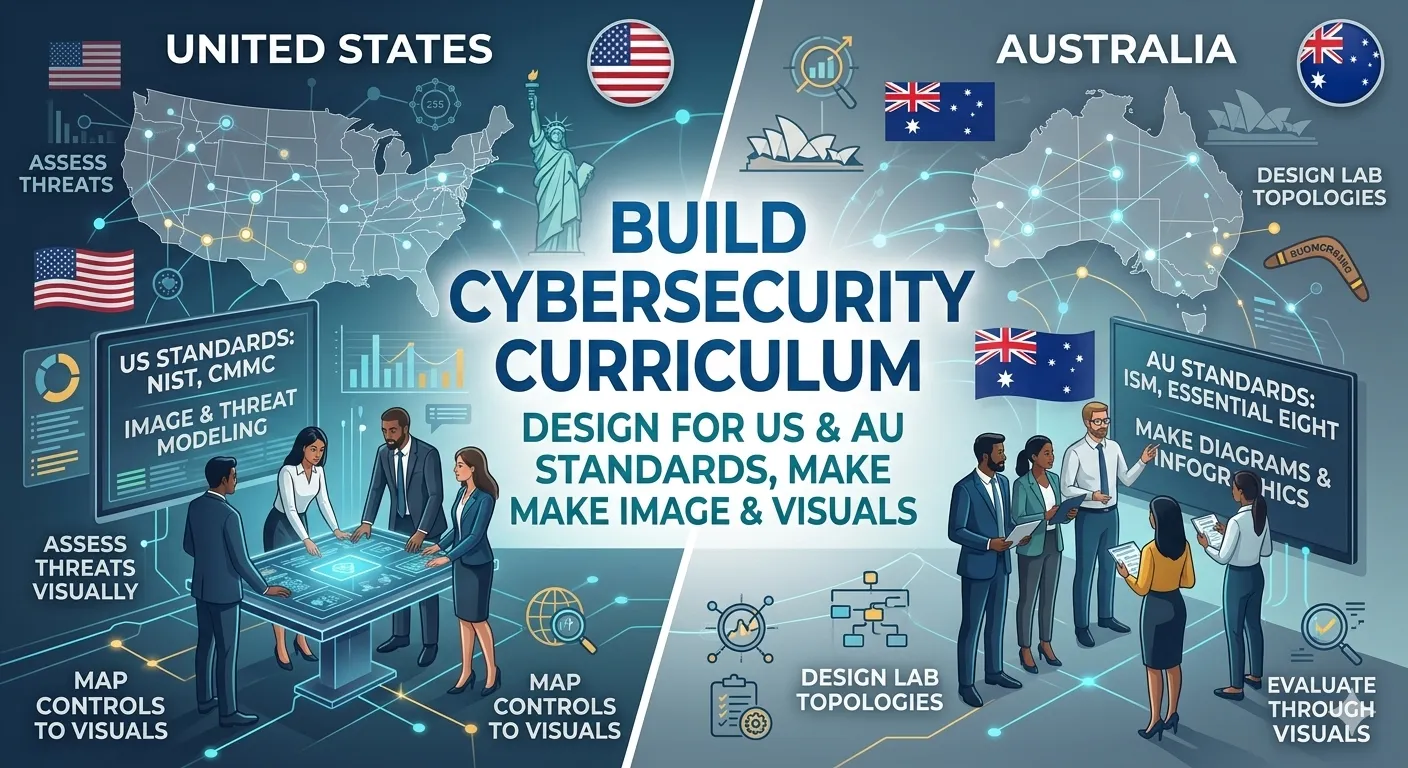
4.1 Cybersecurity Skills Frameworks
Frameworks such as the SPARTA Cybersecurity Skills Framework help educators map roles (e.g., incident responder, security analyst, policy officer) to specific knowledge, skills, and abilities.
Your course can teach:
- How to deconstruct a job description into Cybersecurity learning outcomes.
- How to select topics (e.g., threat modeling, security architecture, governance) based on role maturity, not tradition.
4.2 Aligning with Standards and Capabilities
- National and global Cybersecurity capacity models stress that education, awareness, and training must be part of a broader capacity‑building strategy.
- Studies show that industry‑aligned Cybersecurity curricula produce graduates who solve real security problems faster.
Guide instructional designers to:
- Align modules with industry standards (e.g., NIST, ISO, CIS Controls).
- Use gap analysis between job requirements and current training to justify new modules.
5. Activity Design: From Awareness to Behavior Change
Cybersecurity is about doing, not just knowing. Research on Cybersecurity education and awareness programs shows that one‑off training rarely changes behavior, while sustained, interactive, scenario‑based learning does.
5.1 Scenario‑Based and Experiential Learning
- Experiential learning (Kolb) is used in higher‑education Cybersecurity courses to have learners analyze real incidents, perform mock investigations, and justify decisions.
- Cybersecurity‑awareness activities using gamified quizzes and simulations improve risk perception and secure behavior over time.
Teach instructional designers how to:
- Turn security policies into interactive scenarios (e.g., “You receive a suspicious email: what do you click and what do you report?”).
- Design branching simulations where learners experience consequences of weak password‑hygiene or unpatched systems.
5.2 Micro‑Learning and Ongoing Awareness
- Evidence‑based initiatives recommend integrating Cybersecurity awareness into existing workflows and curricula, not treating it as a standalone module.
- Short, frequent micro‑learning nuggets (e.g., 5‑minute phishing‑spotting drills, password‑strength checkers) reinforce behavior over time.
Suggest templates:
- Monthly “Security Spotlight” modules (e.g., “MFA,” “VPN best practices,” “remote‑work hygiene”).
- Embedded security checks in other courses (e.g., “Before you submit your project, run a privacy‑check checklist”).
6. Assessment Design for Cybersecurity Competence
Traditional multiple‑choice tests are insufficient for Cybersecurity. Research stresses performance‑based and contextualized assessments.
6.1 Types of Assessments
- Knowledge‑check quizzes (MCQs, matching) for basic Cycbersecurity concepts (e.g., types of malware, password best practices).
- Scenario‑based assessments where learners diagnose a simulated breach and document decisions.⁶ ⁸
- Capstone projects such as designing a mini Cybersecurity‑awareness campaign or drafting an incident‑response playbook.
6.2 Rubrics and Formative Feedback
- Studies using constructive alignment emphasize rubrics that explicitly link criteria to Cybersecurity outcomes (e.g., “Explain risk impacts,” “Justify mitigation choices”).
- Frequent, low‑stakes formative feedback improves confidence and reduces errors.
Provide:
- Cybersecurity‑specific rubric templates for writing, incident reports, and policy‑compliance tasks.
- Templates for adaptive feedback (e.g., explaining why a chosen password is weak).
7. Accessibility, Inclusion, and Behavior‑Change Communication
Cybersecurity affects everyone, but not everyone is a technical expert. A Cybersecurity Curriculum Design course must train instructional designers to communicate risk in inclusive, behavior‑friendly language.
7.1 Universal Design for Learning (UDL)
- UDL‑driven Cybersecurity modules use multiple means of representation (text, audio, diagrams), action and expression (simulations, quizzes), and engagement (real‑world scenarios).⁵
- Research on Cybersecurity awareness shows that visual icons, plain‑language checklists, and step‑by‑step guides help diverse learners.
Include:
- Accessibility checklists for Cybersecurity modules.
- Plain‑language templates for policies, incident reports, and awareness emails.
7.2 Behavioral Science and Cybersecurity Communication
- Studies show that effective communication strategies (framing threats concretely, using relatable examples, emphasizing personal impact) improve user compliance.
- Instructional designers can apply nudges (e.g., highlighting “recommended settings,” pre‑populating secure defaults).
Teach:
- How to translate technical vulnerabilities into user‑relevant risks (e.g., “Clicking that link can lock your payroll access”).
- How to design “positive defaults” in training workflows (e.g., auto‑enabling MFA).
8. Tools, Platforms, and Production Workflows
Your course should also address the practical “how” of building e‑learning at scale.
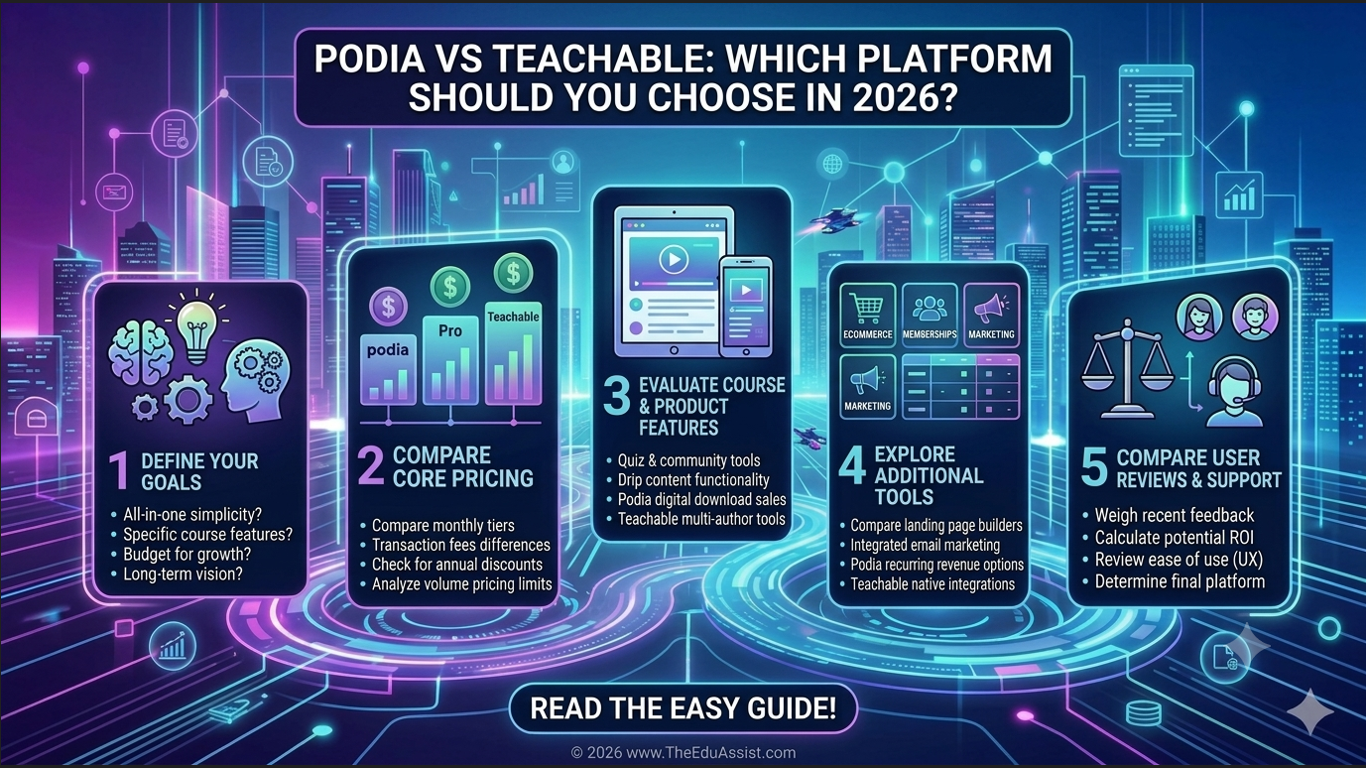
8.1 Authoring and Delivery Platforms
- Examples from the literature show Cybersecurity awareness modules built in Google Classroom, LMS platforms, and web‑based training environments.
- Cybersecurity curricula are often visualized dynamically to show how topics, skills, and roles connect.⁴
Guide instructional designers to:
- Choose authoring tools (e.g., Articulate 360, Captivate, H5P) that support interactive simulations, branching scenarios, and accessibility.⁵
- Integrate gamification features (badges, leaderboards) to reinforce completion.
8.2 Collaboration with Cybersecurity Experts
- Because Cybersecurity evolves rapidly, collaboration with security teams is essential.
- Research stresses interdisciplinary teams (education, IT, HR, legal) to ensure accuracy, compliance, and relevance.
Teach:
- How to conduct subject‑matter interviews with security teams.
- How to document “security facts of record” and update them quarterly.
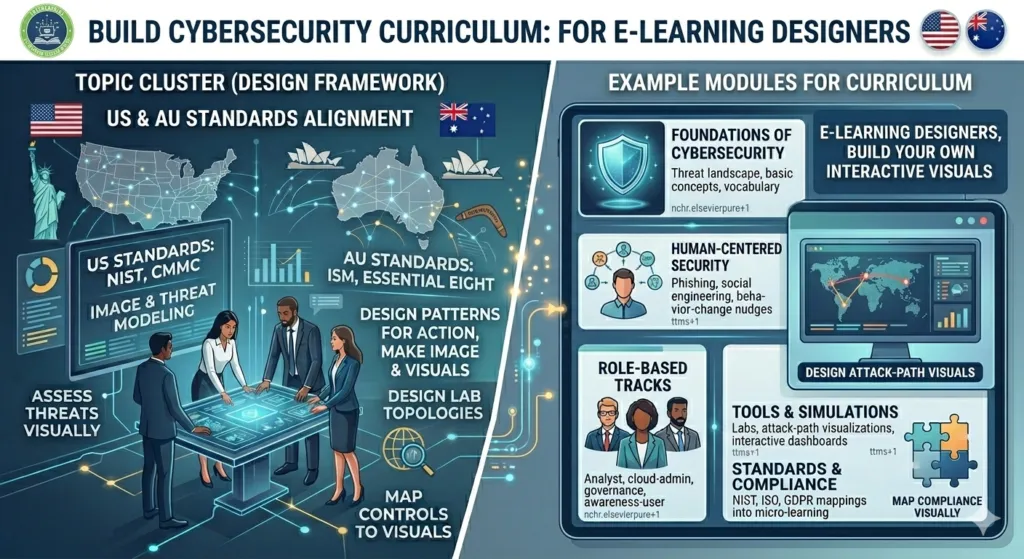
9. Course Structure for e‑Learning Instructional Designers
Here is a suggested module structure (which you can flesh out into full sections):
- Cybersecurity Landscape for Instructional Designers
- Overview of threats, roles, and standards.³
- Applying ID Models to Cybersecurity
- ADDIE/SAM, constructive alignment, multimedia principles.
- Role‑Based and Standard‑Aligned Curriculum Mapping
- Using Cybersecurity skills frameworks and standard
- Scenario‑Based Learning and Simulations
- Phishing simulations, incident‑response drills, micro‑learning
- Assessment and Feedback in Cybersecurity Training
- From quizzes to performance‑based projects.⁶
- Accessibility, Inclusion, and Behavior‑Change Communication
- UDL and behavior‑science nudges.
- Production, Tools, and Maintenance Workflows
- Platforms, version control, and collaboration.
10. Practical Templates and Deliverables
Make the course actionable with ready‑to‑use artifacts:
- Cybersecurity Learning Outcomes Bank
- Curriculum‑mapping templates
- Scenario and simulation templates (phishing, ransomware, data‑leak)
- Accessibility and UDL checklists for Cybersecurity modules
These tools position your course as a practical Cybersecurity Curriculum Design toolkit for e‑Learning instructional designers.
| Metric | Before Generic Training | After Curriculum‑Driven Cybersecurity Training |
|---|---|---|
| Average phishing click‑rate | 45–60% | 15–25% ttms+1 |
| Policy‑awareness score (MCQ) | ~55% | ~80% ttms+1 |
| Incident‑reporting within 1 hour | ~30% | ~60–70% ttms+1 |
| Learner‑rated “confidence in Cybersecurity skills” | Low–medium | Medium–high sciencedirect+1 |
11. How to Position the Course for theEduAssist
Anchor your article around:
- Problem: Generic, non‑inclusive Cybersecurity training that misaligns with real roles and risks.
- Solution: A Cybersecurity Curriculum Design course that blends ID best practices, Cybersecurity research, and behavior‑science.
- Value:
- Enables instructional designers to create role‑specific, standards‑aligned, and behavior‑driven Cybersecurity training.
- Helps organizations reduce risk, improve compliance, and build a Cybersecurity‑aware culture.
| Step in Cybersecurity Curriculum Design | Direct Impact on Learner Behavior |
|---|---|
| Define roles (e.g., “awareness user,” “analyst”) nchr.elsevierpure+1 | More relevant scenarios, higher engagement |
| Use scenario‑based, interactive modules ttms+1 | Better incident‑response and reporting habits |
| Apply constructive alignment and UDL iacis+1 | Deeper understanding, lower cognitive load |
| Implement micro‑learning and simulations ttms+1 | Higher retention and repeated practice |
| Regularly update content with threat‑intelligence ttms+1 | Sustained, real‑world‑aligned awareness |
12. Conclusion: A Call to Action for Instructional Designers
The gap between cybersecurity threats and cybersecurity education will not close by accident. It will close when instructional designers take the lead in designing intelligent, empathetic, and research‑grounded Cybersecurity curricula.
By grounding your Cybersecurity Curriculum Design course in validated models, frameworks, and tools, you empower e‑Learning designers to turn abstract threats into concrete, learnable behaviors—and position your organization as a leader in Cybersecurity education and practice.
References:
Key Research Papers on Cybersecurity Curriculum and e‑Learning
- Cybersecurity Curriculum Design: A Survey – UAE
A comparative overview of existing Cybersecurity curriculum approaches that helps educators design more effective Cybersecurity programs. - Cybersecurity Activities for Education and Curriculum Design: A Survey – UAE University
A recent survey of global Cybersecurity curriculum activities and case studies, useful for instructional designers building role‑based or scenario‑based courses. - Cyber-Security Instructional Technology Design – Georgia Southern University
A paper applying Universal Design for Learning (UDL), Dual Coding, and contiguity principles to Cybersecurity awareness modules in e‑learning environments. - “Cyber-security Instructional Technology Design” – IIS 2019 PDF
An early but still relevant framework for designing learner‑centered Cybersecurity courses using instructional design models and multimedia principles. - Design and Development of a Modular K‑12 Cybersecurity Curriculum – ASEE
A practical example of how to structure modular, role‑adjacent Cybersecurity content that can be adapted for adult e‑learning. - A Reference Point for Designing a Cybersecurity Curriculum for Universities – HAL‑Inria
A scoping‑review‑based reference point for clustering Cybersecurity topics and skills into coherent curriculum modules. - Enhancing Cyber Safety in e‑Learning Environments through Cybersecurity Training – Computers in Human Behavior Reports
A 2025 study linking e‑learning engagement, Cybersecurity awareness, and policy compliance to practical cyber‑safety outcomes in education.
FAQ: Cybersecurity Curriculum Design Course for e‑Learning Instructional Designers
Q1: What is a Cybersecurity Curriculum Design course and why do e‑Learning instructional designers need it?
A Cybersecurity Curriculum Design course teaches instructional designers how to structure, map, and deliver cybersecurity training that actually changes behavior, not just test scores. With cyber threats growing fast, generic awareness modules no longer work. This course gives you a research‑backed framework to design role‑specific, standards‑aligned Cybersecurity learning experiences that reduce organizational risk and strengthen security culture.
Q2: Who is this Curriculum Design course for?
This course is built for:
- e‑Learning instructional designers in corporate L&D, higher education, or government training.
- Cybersecurity training specialists creating awareness or role‑based programs.
- Academics and consultants designing Cybersecurity degree or certificate curricula.
If you already design courses and want to add Cybersecurity as a design domain, this is the program you need.
Q3: How is this different from a regular cybersecurity training course?
Unlike generic cybersecurity training, this is a curriculum design course specifically for instructional designers. Instead of teaching you how to be a cybersecurity analyst, it teaches you how to:
- Map Cybersecurity roles to learning outcomes.
- Align modules with NIST, ISO, and organizational risk profiles.
- Turn policies into interactive scenarios and simulations.
You walk away with a repeatable Cybersecurity curriculum‑design process you can reuse across clients and industries.
Q4: What learning models and best practices will I apply?
You’ll learn how to apply proven instructional‑design and Cybersecurity‑education models, including:
- ADDIE / SAM for rapid, iterative cybersecurity course design.
- Constructive alignment and backward design to ensure every activity supports real security outcomes.
- Universal Design for Learning (UDL) and cognitive load principles to make cybersecurity content accessible and engaging.
These frameworks are backed by research on online Cybersecurity courses and learner‑centered design.
Q5: Will I learn how to design realistic simulations and scenarios?
Yes. A core part of the course focuses on scenario‑based and experiential learning for Cybersecurity:
- How to design phishing simulations, ransomware drills, and incident‑response scenarios.
- How to turn security policies into interactive checklists, branching simulations, and micro‑learning modules.
You’ll also get ready‑to‑use templates you can adapt for your own courses or corporate training programs.
Q6: How do I maketraining engaging for non‑technical learners?
Many learners feel intimidated by cybersecurity jargon. In this course, you’ll learn how to:
- Translate threats into plain‑language risks (e.g., “Clicking this link can lock your payroll access”).
- Use gamification, progress tracking, and micro‑learning to maintain engagement.
- Apply behavior‑science nudges (e.g., “positive‑default settings” and role‑specific prompts) to encourage secure habits.
The result is Cybersecurity training that non‑technical users actually complete and remember.
Q7: Can I use this course to design compliance and awareness programs for my organization?
Absolutely. The course is ideal if your organization needs:
- Cybersecurity awareness programs that go beyond annual one‑off training.
- Compliance‑aligned modules mapped to regulations, frameworks, and internal policies.
You’ll learn how to:
- Conduct a Cybersecurity training needs assessment.
- Break content into small, role‑specific modules.
- Use blended learning (e‑learning, simulations, quizzes) to keep learners engaged and compliant.
Q8: What tools and platforms will I work with in this Cybersecurity Curriculum Design course?
You’ll work with tools and platforms commonly used in modern e‑learning and cybersecurity education:
- Authoring tools (e.g., Articulate 360, Captivate, H5P) for interactive simulations and quizzes.
- LMS and LXP platforms to deliver role‑based Cybersecurity tracks.
- Virtual labs and sandbox environments when designing more technical modules.
You’ll also learn how to collaborate with security teams using version‑controlled content and shared “facts of record” for your Cybersecurity materials.
Q9: How long is the course, and is it self‑paced?
The Cybersecurity Curriculum Design course is designed as a self‑paced, project‑based program that typically takes 4–6 weeks to complete, depending on your prior experience. You’ll:
- Watch short, focused video lessons.
- Apply what you learn in guided design sprints (e.g., mapping a role‑based Cybersecurity track).
- Get feedback‑ready templates and checklists you can use immediately with clients or internal stakeholders.
Q10: Will I get a certificate or credential after finishing?
Yes. Upon successful completion, you’ll receive a Cybersecurity Curriculum Design certificate from theEduAssist that validates your ability to:
- Design learner‑centered, role‑based Cybersecurity courses.
- Apply instructional‑design models and multimedia principles to Cybersecurity content.
- Develop engaging simulations, assessments, and micro‑learning modules.
This credential is ideal for instructional designers, L&D specialists, and cybersecurity training leads who want to stand out in the growing field of Cybersecurity education and training.
Authored By: Atiqa Sajid http://www.linkedin.com/in/atiqa-sajid-747b57137